Table of Contents
Key Takeaways
- Evolving Threat Landscape: Cyber attacks in 2026 are more sophisticated than ever, making traditional security insufficient. PAM provides a critical layer of defense against advanced persistent threats, ransomware, and insider attacks.
- Core PAM Functionality: Modern PAM solutions go beyond basic password management, offering features like just-in-time access, session monitoring, multi-factor authentication, and robust auditing to secure privileged accounts.
- Strategic Integration is Key: For optimal protection, PAM must be seamlessly integrated with existing cybersecurity frameworks, including identity and access management (IAM), security information and event management (SIEM), and vulnerability management systems.
- AI and Machine Learning’s Role: Artificial intelligence and machine learning are revolutionizing PAM by enabling proactive threat detection, behavioral analytics, and automated responses, significantly enhancing defensive capabilities.
- Continuous Optimization: Effective PAM implementation requires continuous monitoring, regular policy review, and adaptation to new threats, alongside strict adherence to best practices like role-based access control.
In the dynamic digital landscape of 2026, organizations face an unprecedented barrage of sophisticated cyber threats. The era of simple perimeter defenses is long past; today’s attackers are highly skilled, adaptive, and relentless, constantly seeking new vulnerabilities to exploit. These evolving tactics often target the most critical access points within an enterprise: privileged accounts. The consequences of a successful breach are severe, ranging from devastating data loss and operational disruption to significant financial penalties and irreversible reputational damage. As evidenced by IBM’s 2023 report, the average cost of a data breach escalated to an all-time high of $4.45 million, underscoring the urgent need for robust security measures.
Traditional cybersecurity approaches, while still vital, are frequently outmatched by the ingenuity of modern cybercriminals. To truly safeguard their invaluable digital assets and maintain their integrity in an increasingly hostile online environment, companies require an elevated form of protection. This is where Privileged Access Management (PAM) emerges as a cornerstone of advanced cybersecurity strategy. PAM is not merely a tool; it’s a comprehensive framework designed to control, monitor, and secure all human and non-human privileged access across an organization’s IT infrastructure. It acts as an unbreakable digital cover, ensuring that only authorized entities can access the most sensitive systems and data, effectively neutralizing many of the advanced threats that bypass conventional defenses. This article delves into How Modern PAM Solutions Protect Against Advanced Cyber Attacks, exploring its evolution, key features, integration strategies, and the transformative role of emerging technologies like AI and machine learning.
Understanding Privileged Access Management (PAM)
Privileged Access Management (PAM) functions as a critical cybersecurity safeguard, acting as a digital shield for an organization’s most valuable information and systems. At its core, PAM is designed to protect specialized accounts that possess elevated permissions—often referred to as ‘privileged accounts.’ These accounts are the keys to the kingdom, capable of accessing critical infrastructure, sensitive data, and administrative functions across a company’s network. For cyber attackers, these privileged accounts represent the ultimate prize, akin to gem chests brimming with invaluable information, making them prime targets for sophisticated breach attempts.
With a robust PAM framework in place, organizations gain unparalleled control over these powerful accounts. It allows them to establish strict access rules, dictating precisely who can access what, when, and under what conditions, based on their defined roles and responsibilities. Beyond mere access control, PAM solutions are adept at detecting and flagging suspicious activity that could indicate an ongoing hacking attempt or an insider threat. This proactive monitoring is crucial for identifying unauthorized access patterns or deviations from normal behavior, allowing security teams to intervene before significant damage occurs.
By implementing comprehensive PAM tools, businesses significantly strengthen their defensive posture. They make it exponentially harder for malicious actors, whether external cybercriminals or rogue insiders, to compromise critical systems. It’s akin to fortifying a digital stronghold with the strongest possible locks, surveillance systems, and guard protocols, ensuring the utmost security for an organization’s most sensitive digital assets.
Important things to know about Privileged Access Management are:
- Restricting access to only authorized users, ensuring the principle of least privilege.
- Monitoring and recording all privileged account activity for comprehensive auditing and forensics.
- Implementing multi-factor authentication (MFA) for added security layers, making unauthorized access significantly more difficult.
- Automating password management and rotation for privileged credentials to eliminate common vulnerabilities.
- Providing just-in-time (JIT) access, granting privileges only for the duration of a specific task.
The Landscape of Cyber Threats in 2026: How Modern PAM Solutions Protect Against Advanced Cyber Attacks
In 2026, the cyber threat landscape continues to evolve at an alarming pace, presenting significant and multifaceted challenges for organizations across all sectors. The sheer volume and sophistication of new malicious software variants discovered daily underscore the dynamic nature of this threat environment. To effectively protect against future compromises and understand How Modern PAM Solutions Protect Against Advanced Cyber Attacks, it is crucial to recognize the prevailing types of attacks and their origins.
Common attack vectors remain prevalent but have become increasingly sophisticated. These include highly personalized phishing campaigns, targeted whaling attacks aimed at senior executives, polymorphic malware designed to evade detection, elaborate social engineering schemes, devastating ransomware-as-a-service operations, and distributed denial-of-service (DDoS) attacks that can cripple online services. According to Verizon, email remains a primary delivery mechanism, accounting for 94% of malware propagation, highlighting a persistent vulnerability.
Malicious actors are perpetually refining their tactics, continuously discovering new methods to bypass conventional security measures. These adversaries leverage advanced techniques such as zero-day exploits, supply chain attacks, and sophisticated credential theft methods that often target privileged accounts. The convergence of artificial intelligence with offensive cyber capabilities is also leading to more autonomous and evasive threats, capable of adapting to defenses in real-time.
Consequently, organizations must adopt a proactive and adaptive stance in their cybersecurity strategies. As technology advances, so too do the complexities and destructive potential of cyber attacks. This escalating threat necessitates robust and intelligent defensive capabilities. It is precisely why it is paramount for companies to fortify their security posture by implementing strong and modern Privileged Access Management (PAM) systems. These systems are specifically engineered to address and mitigate the challenges posed by this new generation of threats, playing a vital role in how modern PAM solutions protect against advanced cyber attacks. By securing the most vulnerable points of entry—privileged access—PAM becomes an indispensable component in the ongoing battle against cybercrime.
Key Features of Modern PAM Solutions
Modern Privileged Access Management (PAM) solutions are far more comprehensive than their predecessors, equipped with a suite of sophisticated features designed to counter the intricacies of advanced cyber attacks in 2026. These capabilities move beyond simple password vaults to create an adaptive and intelligent defense perimeter around an organization’s most sensitive assets.
Privileged Access Management (PAM): At its core, modern PAM is about meticulous control. It acts as a gatekeeper, meticulously governing who can perform specific actions and access particular resources based on a finely tuned role-based access control (RBAC) model. This ensures that users, whether human or machine, are granted the absolute minimum level of access required to perform their assigned tasks—a principle known as “least privilege.” This granular control is paramount in preventing harmful attacks originating from within, commonly known as insider threats, where authorized users might inadvertently or maliciously misuse their privileges. By limiting the blast radius of any potential compromise, PAM significantly reduces the risk profile of the entire organization.
Multi-Factor Authentication (MFA): Another indispensable feature of modern PAM is Multi-Factor Authentication (MFA). Imagine securing your most precious digital assets not just with a single password, but with a combination lock that requires a secret code and a unique, time-sensitive key from a separate device. That’s the power of MFA. It demands multiple forms of verification before granting access, making it exponentially more difficult for cybercriminals to breach accounts even if they manage to steal or phish credentials. By adding this extra layer of security—often combining something you know (like a password), something you have (like a phone or token), and sometimes something you are (like a fingerprint)—MFA acts as a formidable barrier against sophisticated credential theft attacks.
Session Monitoring and Recording: Modern PAM tools extend their protective capabilities beyond access control with advanced session monitoring and recording. This feature functions like a vigilant superhero sidekick, continuously observing and logging all activity performed during a privileged session in real-time. Every command executed, every file accessed, and every configuration change made is meticulously recorded. This constant oversight serves multiple critical purposes: it can detect suspicious behavior as it happens, allowing security teams to intervene immediately and stop an attack in progress. Furthermore, the detailed recordings provide an invaluable audit trail, essential for forensic analysis post-incident, compliance reporting, and proving adherence to security policies. It’s a transparent and accountable way to manage high-stakes access, ensuring that any malicious or unauthorized actions are quickly identified and addressed.
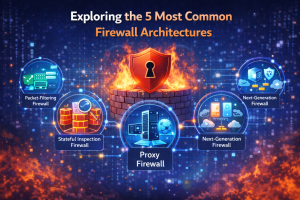
Integrating PAM with Your Existing Cybersecurity Strategy
Integrating a modern Privileged Access Management (PAM) solution seamlessly into an organization’s existing cybersecurity strategy is not merely an optional step but a critical imperative for comprehensive defense in 2026. PAM should not operate in isolation; its true power is unlocked when it works in concert with other security tools and processes. This synergy enhances the overall security posture, providing a more robust and adaptive shield against advanced cyber threats. Here’s a structured approach to achieving effective integration, highlighting How Modern PAM Solutions Protect Against Advanced Cyber Attacks through a holistic security framework.
01 Check Your Security: Conduct a Comprehensive Security Audit.
This initial step is foundational. Before deploying any new solution, organizations must gain a clear understanding of their current cybersecurity landscape. This involves a thorough examination of existing security controls, policies, vulnerabilities, and potential attack vectors. Identify any weak spots, legacy systems, or processes that are particularly susceptible to privileged account compromise. This audit should cover identity and access management (IAM) practices, network security, endpoint protection, and data governance. Pinpointing these areas of concern will guide the PAM implementation and ensure it addresses the most critical gaps.
02 Match PAM with Your Goals: Align PAM with Broader Security Objectives.
The chosen PAM solution must be compatible and interoperable with other elements of your cybersecurity ecosystem. It should integrate smoothly with your Identity and Access Management (IAM) system for user provisioning, your Security Information and Event Management (SIEM) system for centralized logging and threat intelligence, and your vulnerability management tools for risk assessment. The goal is to create a unified security fabric where PAM enhances the capabilities of existing defenses, rather than creating new silos. This strategic alignment ensures that PAM actively contributes to your organization’s overarching security objectives, ultimately amplifying your protection capabilities and helping you achieve optimal security results.
You can also look at Use Bitcoin for a more focused take on the software side of the topic.
That discussion also overlaps with Does Stand, which covers the security angle in more detail.
03 Keep an Eye on Things: Implement Continuous Monitoring and Maintenance.
Deployment is just the beginning. Effective PAM integration demands ongoing vigilance. Continuously monitor your PAM solution’s performance, user activity, and system alerts. Regularly review and update access policies, privileged credentials, and system configurations to adapt to changing operational needs and evolving threat landscapes. Staying abreast of the latest PAM features and security patches is crucial. This proactive monitoring and maintenance regime not only helps in keeping pace with new threats but also ensures the PAM system remains effective, providing peace of mind by maintaining a consistently strong defensive posture.
04 Use Modern PAM: Leverage Advanced Features for Enhanced Defense.
Embrace the full spectrum of capabilities offered by modern PAM solutions. Beyond basic password management, this includes features like just-in-time (JIT) access, which grants temporary privileges only when needed; session isolation, which creates a secure environment for privileged tasks; and behavioral analytics, which uses machine learning to detect anomalous activity. By fully leveraging these advanced features, organizations can significantly strengthen their defenses against the most sophisticated cyber threats. Modern PAM provides enhanced visibility into privileged activities, greater control over access, and more effective risk management, making it an indispensable component of a resilient cybersecurity strategy in 2026.
Case Studies: Successful PAM Implementations Against Cyber Attacks
Understanding how Privileged Access Management (PAM) works in theory is one thing, but seeing its effectiveness in real-world scenarios against sophisticated cyber threats provides tangible proof of its value. Here are some compelling case studies illustrating How Modern PAM Solutions Protect Against Advanced Cyber Attacks for various organizations.
Company MANE: Using a new high-tech security system called Privileged Access Management (PAM), Company MANE stopped a targeted cyber attack to break into its important computer systems.
Moreover, this PAM system monitored who was trying to access the most important parts of the network and stopped anyone who shouldn’t be there.
Organization MyVest: After several instances of hackers getting into their systems because they didn’t manage their important passwords properly, Organization MyVest decided to make a big change. They put in place a detailed plan using PAM.
This plan included the following:
- Changing passwords regularly.
- Recording what people were doing when they logged in.
- Keeping a close watch on everything that happened on their network.
Thanks to these changes, they could spot and stop bad guys trying to mess with their systems.
Enterprise Wynn: Facing serious threats from tricky hackers, Enterprise Wynn did something smart. They added special computer programs called machine learning algorithms to their PAM system.
These smart programs could figure out when something bad happened on their network by spotting unusual patterns. Then, they could quickly block the bad guys or activate extra security measures before things got really bad.
Emerging Technologies in PAM: AI and Machine Learning
The evolution of Privileged Access Management (PAM) is inextricably linked with the advancements in artificial intelligence (AI) and machine learning (ML). These emerging technologies are not just enhancing PAM solutions; they are fundamentally transforming How Modern PAM Solutions Protect Against Advanced Cyber Attacks by introducing unprecedented levels of automation, precision, and predictive capabilities into cybersecurity.
AI and ML improve threat detection: Advanced AI programs can analyze a large amount of data and find patterns that might indicate a cyber threat. This helps PAM solutions determine whether something bad is going on.
ML helps understand user behavior: With machine learning, PAM solutions can learn how users usually behave and spot when something’s wrong.
Using AI and machine learning in PAM is important for stopping tricky cyber attacks. These cool technologies can strengthen companies’ security and prevent problems before they become major.
Best Practices for Optimizing PAM in Your Organization
To fully leverage the capabilities of Privileged Access Management (PAM) and ensure it effectively defends against the advanced cyber threats of 2026, organizations must adopt a set of best practices. Optimizing your PAM implementation means not only deploying the technology but also establishing robust processes and maintaining continuous vigilance. These practices are fundamental to maximizing the security benefits of PAM and truly understanding how modern PAM solutions protect against advanced cyber attacks.
Role-Based Access Control
Use role-based access control (RBAC) to ensure users only have access to what they need. This lowers the chance of important accounts being hacked.
Regular Monitoring
Regularly check and change what users can do to match their jobs. This prevents people from doing things they shouldn’t and makes it harder for cyber bad guys to attack.
Multi-Factor Authentication
Multi-factor authentication (MFA) adds an extra layer of security. It makes it much harder for someone to get in, even if they know the password.
If you do these things, your organization can improve the performance of its Privileged Access Management (PAM) system. This will help keep your digital assets safe from changing threats.
Future Outlook: Evolving Cyber Threats and PAM Innovation
- Cyber Threats Keep Changing:
The world of cyber threats is always shifting, with new tricks and tech constantly popping up.
Companies must keep up with these changes by improving their security to stay safe.
- Big Threats Need Big Solutions:
Fancy cyber attacks, like advanced persistent threats (APTs), are a big deal for companies.
To deal with them effectively, we need smart solutions like Privileged Access Management (PAM).
- Getting Smarter with PAM:
PAM solutions are always getting better at fighting off tricky cyber threats. The new ones are super smart, using AI and fancy controls to keep the bad guys out.
With cyber crooks getting smarter, it’s important to keep PAM up to date to stay safe.
As cyber-attacks get smarter, old ways of staying safe aren’t enough anymore. New PAM ideas use things like smart authentication, computer learning, and always watching out for unusual stuff to keep bad guys away.
Since businesses use computers a lot, it’s super important to have strong PAM tools to keep things safe and make customers feel secure. To keep up with tricky hackers, it’s essential to use these new PAM ideas to stay safe in the future.
FAQs (Frequently Asked Questions)
What is Privileged Access Management (PAM)?
Privileged Access Management (PAM) is a cybersecurity solution that helps organizations protect their most critical data and systems by controlling and monitoring access to privileged accounts. These accounts have elevated permissions and can access sensitive information, making them prime targets for hackers.
Why is PAM important for cybersecurity?
PAM is essential for cybersecurity because it helps prevent unauthorized access to sensitive data and systems. By managing and monitoring privileged accounts, organizations can reduce the risk of data breaches and insider threats, safeguarding their valuable assets and maintaining regulatory compliance.
How does PAM protect against advanced cyber attacks?
PAM protects against advanced cyber attacks by implementing stringent access controls, monitoring privileged account activity in real-time, and detecting anomalies that may indicate a security threat. By leveraging technologies like AI and machine learning, PAM solutions can enhance threat detection and response capabilities.
References
- IBM. (2023). Cost of a Data Breach Report 2023. IBM Security.
- Verizon. (2023). Data Breach Investigations Report 2023.